Sonar's latest blog posts
State of Code Developer Survey report: The current reality of AI coding
Sonar analyzes over 750 billion lines of code every day. This gives us a unique, high-level view of the state of code quality and security across the globe.

Five SonarQube Cloud features for developers that want Code Quality
Whether you’re working on a new project or an existing one, you might think of Code Quality as an ideal, somewhere far out of reach. Let’s go over 5 key features that make SonarQube Cloud the perfect tool for developers and development teams to deliver Code Quality consistently and efficiently, without disrupting the existing development workflow.
Read Blog >
Securing Developer Tools: A New Supply Chain Attack on PHP
What is your worst supply chain nightmare and why is it somebody that could take over all the PHP packages at once? Let's deep dive into how we could demonstrate it!
Read Blog >
Get new blog posts delivered directly to your inbox!
Stay up-to-date with the latest Sonar content. Subscribe now to receive the latest blog articles.

Our journey toward accessibility
When you think about your typical workday, how much time do you spend working on a computer? How hard would it be for you to perform your job if you did not have access to a computer?
Read Blog >
Securing Developer Tools: OneDev Remote Code Execution
We recently discovered several vulnerabilities in OneDev 7.2.9 that allowed attackers to fully compromise a server and even break out of a Docker environment.
Read Blog >
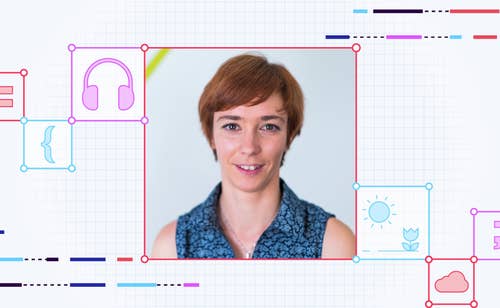
Interview with a SonarSource Developer
Curious about life as a Developer at SonarSource? Join us as we discuss changes in the world of programming, the importance of Security, and writing code with SonarQube Cloud Backend Developer Claire Villard.
Read Blog >

The evolving landscape of open source licensing: What you need to know
In this post we will cover why it’s important to know what licenses accompany the open source in use at your organization
Read article >
The Power of Code Quality
Code Quality—a term you may have casually used or heard before but may not have synthesized or internalized its true essence. In this post, learn what Code Quality is and why it matters.
Read Blog >

WordPress Core - Unauthenticated Blind SSRF
Our security researchers were surprised to discover a low-hanging code vulnerability in WordPress Core that we will discuss in this blog post.
Read Blog >
You’re 3 minutes away from clean Java pull requests!
In this blog, we demonstrate how you can get started with SonarQube Cloud in less than 3 minutes and ensure all new Java pull requests are clean, every time.
Read Blog >

Sonar Streamlines the Race to Release
Knowing if your latest release candidate is built with Code Quality doesn’t have to be a guessing game. With Sonar at your side, you’ll know that every new line, every PR and every build is clean.
Read Blog >

Securing Developer Tools: Argument Injection in Visual Studio Code
In the third part of our Securing Developer Tools series, we look at a critical vulnerability that affects one of the most popular code editors: Visual Studio Code.
Read Blog >