Sonar's latest blog posts
State of Code Developer Survey report: The current reality of AI coding
Sonar analyzes over 750 billion lines of code every day. This gives us a unique, high-level view of the state of code quality and security across the globe.

PHP Supply Chain Attack on Composer
We recently discovered a vulnerability in Composer, the main package manager for PHP, and were able to use it to take over the central repository, packagist.org.
Read Blog >
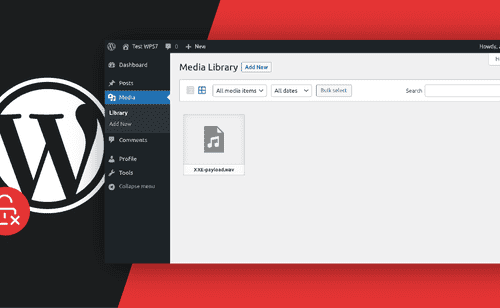
WordPress 5.7 XXE Vulnerability
In this blog post we analyze a XXE vulnerability that our analyzers discovered in WordPress, the most popular CMS, and what PHP 8 developers can learn from it.
Read Blog >
Get new blog posts delivered directly to your inbox!
Stay up-to-date with the latest Sonar content. Subscribe now to receive the latest blog articles.

Code Vulnerabilities in NSA Application Revealed
Our security research team discovered multiple code vulnerabilities in the NSA's Java application Emissary. Find out more about these issues and related attacks.
Read Blog >
Mono-repository support for Bitbucket Cloud now available for SonarQube Cloud!
Last September, we announced that mono-repository support was added for GitHub and Azure DevOps Services. The good news is: mono-repository support is now also available for Bitbucket Cloud! See what it brings and how you can configure it in SonarQube Cloud.
Read Blog >

MyBB Remote Code Execution Chain
Today SonarSource is pleased to share a guest contribution to our Code Security blog series about learnings from a chain of serious vulnerabilities in MyBB.
Read Blog >

Hack the Stack with LocalStack: Code Vulnerabilities Explained
Our vulnerability researchers found critical code vulnerabilities in a popular Python application that can be exploited remotely, even when the application instance is hosted locally.
Read Blog >

Crafting regexes to avoid stack overflows
Due to the way regular expression matching is implemented in Java (and many other languages/libraries), matching a pattern may - depending on the regex - require stack space proportional to the length of the input. This means large inputs could cause the program to crash with a `StackOverflowException` when you try to use the regex.
Read Blog >

Setting the right (regex) boundaries is important
Regular expressions pack a lot of power into terse little packages and unfortunately that introduces a lot of room for error. This post talks about regex boundaries, another feature that can lead to bugs when used incorrectly, and a rule of ours that can help you avoid such issues. it also covers about complexity and maintainability in regular expressions and our rule to help you find regular expressions that are too complex.
Read Blog >

Regular expressions present challenges even for not-so-regular developers
Regular expressions are a concise and powerful tool for processing text. However, they also come with a steep learning curve and plenty of opportunities to make mistakes. This is the first in a series of posts about some specific regex pitfalls.
Read Blog >

What I learned from the Server Side Public License
When the Server Side Public License (SSPL) was submitted to the Open Source Initiative (OSI), many people criticized it, and the license was eventually withdrawn.
Read article >

Code security: now there's a tool for developers
Hey SonarQube Server and SonarQube Cloud users! You now have a tool to own Code Security! SonarSource has been hard at work for the last year to give you the tooling to review and improve your code security. We're glad to say that today you have at your fingertips unmatched precision and performance in SAST (Static Application Security Testing) analysis for five languages and counting.
Read Blog >