Sonar's latest blog posts
State of Code Developer Survey report: The current reality of AI coding
Sonar analyzes over 750 billion lines of code every day. This gives us a unique, high-level view of the state of code quality and security across the globe.

Codoforum 4.8.7: Critical Code Vulnerabilities Explained
We analyze the root cause of three critical security vulnerabilities that enabled a complete board take over, and how to correctly prevent these in your code.
Read Blog >
About the recent code leaks from SonarQube Server instances
On July 27th 2020 we learned through media coverage that Till Kottmann was able to access non open-source source code from various companies. This is our public response to the incident.
Read Blog >
Get new blog posts delivered directly to your inbox!
Stay up-to-date with the latest Sonar content. Subscribe now to receive the latest blog articles.
Take Control of Code Quality with SonarQube Server Pull Request Decoration in Your Workflow
How do you write super Code Quality without disrupting your workflow? Join me as I show you how SonarQube Server Pull Request Decoration gets you there!
Read Blog >

How Google manages open source
The Google monorepo has been blogged about, talked about at conferences, and written up in Communications of the ACM.
Read article >

Package signing across package managers
Recently I looked at the state of 2FA support across package managers. 2FA adds a layer of security by requiring two sources of authentication from maintainers when publishing packages.
Read article >
Apache Kylin 3.0.1 Command Injection Vulnerability
We discovered a severe command injection vulnerability in Apache Kylin that allows malicious users to execute arbitrary OS commands.
Read Blog >

SonarSource acquires RIPS Technologies
Teams will be joining forces in building best-in-class Static Application Security Testing (SAST) products that help development teams and organizations deliver more secure software.
Read Blog >
Exploiting Hibernate Injections
Hibernate is among one of the most commonly found database libraries used in Java web applications, shipping with its own query language. This technical post will teach you how to detect and exploit Hibernates very own vulnerability: The HQL Injection.
Read Blog >
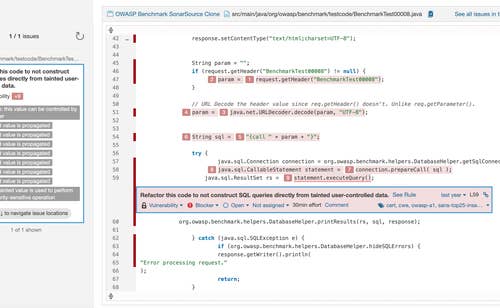
What is 'taint analysis' and why do I care?
In large systems, finding the bad actors is easier said than done. First you have to find all the places you accept data from users, and then you have to sanitize the data before you use it. The hard part is making sure you've found all the sources of user data and intervened before any kind of use. That's where taint analysis comes in.
Read Blog >

The state of the copyleft license
In this post, I want to go a little deeper into one important type of license: those that require sharing of modifications under certain conditions, often called “copyleft” or “reciprocal” licenses
Read article >

WordPress <= 5.2.3: Hardening Bypass
This blog post details an authenticated Remote Code Execution (RCE) vulnerability in the WordPress core that bypasses hardening mechanisms. The vulnerability is present in the WordPress core in versions prior to 5.2.4
Read Blog >